Top 10 Cybersecurity Facts & Stats in 2026
HighSpeedOptions prides itself on providing honest, quality content. While we may be compensated when you make a purchase through links on our site, all opinions are our own. Here's how we make money.
Table of Contents
It’s just a fact: if you use the internet, you are vulnerable to many types of cybercrimes. It doesn’t matter who your internet service provider is or what type of internet connection you have.
And to compound the issue, technology and cybercrime go hand in hand–as the number of devices connected to the internet increases, so does cybercrime.
Cybercrime causes trillions of dollars in damages and devastates individuals and businesses around the world each year. According to a 2024 FBI report, cybercrime losses increased by 33%, totaling over $16.6 billion, based on 859,532 complaints. And that likely doesn’t include losses due to unreported crimes. And it shows no signs of slowing down. In fact, according to this Gallup Poll, Americans now worry more about suffering a cyber-attack than they do about being a victim of a violent crime.
No matter your internet lifestyle, you need to be aware of potential online threats and security weaknesses. Check out these 10 cybersecurity statistics; from user error to data breaches, you’ll learn how widespread cybercrime really is and which online traps to avoid at all costs.
Many providers include internet security in their services, helping to keep you and your family safe from many cybersecurity threats.

Key Findings
- 68% of cyber breaches involve human error
- 15% of breaches stem from phishing emails
- Weak passwords contribute to ~30% of global data breaches
- 85% of cyberattacks are financially motivated
- 23% of smartphones have at least one high-risk or sideloaded app installed
- Over 8 million DDoS attacks were observed in the first half of 2025 alone
- Connected IoT devices are projected to reach ~20B in 2025 and 40B by 2030
- Over 8 million DoS attacks were recorded in the first half of 2025
- VPN adoption is growing — about 1 in 3 U.S. users (32%) now use a VPN
- Global cybercrime costs are projected to hit $10.5 trillion annually by 2025
1. Human error accounts for 68% of all cyber breaches
According to Verizon’s 2024 Data Breach Investigations Report, 68% of all successful cyber breaches are caused by human error. The most common errors people make include using weak passwords or accidentally sending sensitive data to the wrong person. After these, poor update hygiene, downloading and using unverified apps are common human errors.
Why it matters for you: Even a simple mistake like misaddressing an email or reusing a password can put your personal accounts or work data at risk.
How to Reduce Human Error in Cyberattacks
Double-check recipients. Before sending sensitive information, verify the email address or phone number.
Slow down under pressure. Phishing often works by creating urgency. Take a moment to verify before acting.
Report suspicious activity. If you notice a suspicious email or login attempt, report it to IT/security immediately.
A good rule of thumb: If you weren’t expecting it, don’t click it. Whether it’s a link, an attachment, or a request for information, pause and verify through another trusted channel before taking action.

2. Many successful cyber attacks stem from phishing emails
Phishing emails are the source of about 15% of all cyberattacks or breaches. The Anti-Phishing Work Group observed over a million phishing attacks in Q1 2025, the largest since 2023. And KnowBe4 reports a 17% increase in phishing emails between September 2024 and February 2025.
Disguised as someone you may know, phishing emails try to trick users into downloading malware attachments or entering passwords
Why it matters for you: Phishing scams are designed to trick you — not your IT team — meaning your inbox is often the first line of defense..
How to Identify Phishing Emails
Suspicious sender address. The display name looks familiar, but the actual email address is slightly off (extra letters, wrong domain, strange characters).
Generic greeting. “Dear Customer” or “Hello User” instead of using your real name.
Urgency or scare tactics. Phrases like “Act now,” “Immediate action required,” or threats of account suspension.
Mismatched URLs. Hover over a link: does the address match the supposed sender’s domain? If not, it’s likely a phishing attempt.
Unusual requests for sensitive info. Legitimate companies rarely ask for passwords, banking details, or verification codes via email.
A good rule of thumb: If something feels off, don’t click. Instead, go directly to the company’s official website or app to verify.
3. Weak passwords make up 30% of global data breaches
Weak passwords cause about a third of the world’s data breaches. It’s easy to fall into the habit of creating weak, more memorable passwords given how often various devices, apps, and websites prompt for password changes. It doesn’t help that, according to NordPass, some of the most common passwords still used today include 123456, password, and admin.
Why it matters for you: If you’re still using short or repeated passwords, a hacker could access multiple accounts with one stolen login.
Tips for More Secure Passwords
Avoid personal info. Don’t use names, birthdays, addresses, or common words that attackers can easily guess.
Use passphrases. Combine random words into a memorable phrase (e.g., “PurpleDog!Runs4Coffee$Moon”).
A Good Rule of Thumb: If you can easily remember it, it’s probably too weak — let a password manager do the remembering.

4. 85% of all cybersecurity attacks are financially motivated
According to Verizon’s 2025 DBIR report, the number one motivator for all cybersecurity attacks in the world is money (85%). With online banking and digital wallets increasing in popularity, the internet is ripe for financially motivated hackers. This means the need for cybersecurity and strong password protection is crucial for users. Internet service providers like Earthlink offer solutions to help secure your internet connection from the get-go.
Why it matters for you: Most attacks target money — from draining bank accounts to stealing credit card info — making your finances a prime target.
Tips to Reduce Financially Motivated Cyber Attacks
Verify payment requests. Always double-check invoices, wire transfers, or requests for funds — especially if they involve urgency or a change in account details.
Stay alert to phishing. Be cautious with emails or texts asking for login details, account resets, or financial info. Hover over links before clicking.
Monitor accounts regularly. Set up alerts on bank and credit card accounts to catch unusual transactions quickly.
A good rule of thumb: Never trust a money-related request at face value — verify it through a second channel. (e.g., call your bank or the requester directly before sending funds or sharing information).
5. Nearly 1 in 4 mobile devices have a high-risk app installed
According to the Zimperium 2025 Global Mobile Threat Report, about 23% of smartphones have at least one high-risk or “sideloaded” app installed. Sideloaded apps are applications installed on a device from sources other than its official app store. Kaspersky reports blocking about 33 million unwanted mobile software attacks in 2024.
Whether you use an iPhone or Android device, make sure it’s a trusted app before downloading.
Why it matters for you: That free app download could secretly be spying on your data or giving hackers an open door into your phone.
Tips to Prevent Sideloaded / Unwanted App Risks
Turn off “install from unknown sources.” On Android, disable the option that allows apps from outside official stores.
Check the developer’s reputation. Before installing, verify the developer name, number of downloads, and reviews. Avoid apps from unknown publishers.
Review app permissions. Be wary of apps asking for unnecessary access (e.g., flashlight apps requesting contacts or the microphone).
Audit your apps regularly. Delete apps you no longer use. Fewer apps mean fewer potential vulnerabilities.
A good rule of thumb: If you don’t know the source, don’t install the app.

6. Millions of cyberattacks happen daily
NETSCOUT reported more than 8 million DDoS attacks globally in the first half of 2025. The report breaks out more than 3.2 million of those attacks in Europe, the Middle East, and Africa (EMEA). So, the recent data shows that the volume of attacks is far larger than the old “one attack every 39 seconds” stat. That comes from a study by the University of Maryland, and it’s no longer a reliable gauge of today’s scale.
These numbers make it clear: attacks now happen continuously, every second of the day. They’re a constant threat, targeting businesses, organizations, and individuals around the world.
Why it matters for you: Attacks aren’t rare — they’re constant, meaning your personal data is always a potential target if you’re not protected.
Tips to Reduce Cyberattacks
Limit personal information online. Oversharing on social media (location, birthdays, employer details) gives attackers material for spear-phishing or identity theft.
Segment your home/work network. Use a separate Wi-Fi network for smart devices (IoT) so that if one gets compromised, it doesn’t expose your computer or phone.
Be cautious with browser extensions. Only install extensions from trusted developers, and prune them regularly — malicious or abandoned ones are a common entry point.
Log out of accounts on shared or public devices. Don’t leave active sessions open in browsers; always sign out after use.
A good rule of thumb: The less exposed you are online, the fewer doors attackers can open.
7. Connected IoT devices to exceed 40 billion by the end of 2030
According to IoT Analytics, there were 16.6B connected IoT devices at the end of 2023, 18.8B by the end of 2024, and a projected ~40B by 2030. Many 2025 forecasts now sit in the ~20B range. Cybercrime rates are inevitably related to two things: the world population and the number of connected IoT devices. The more people and devices connected to the internet, the more opportunities a hacker has to tap into your personal data.
To elevate your security and your privacy, we strongly encourage you to hide your IP address. Providers, such as Xfinity, include network security that can protect any wired or wireless device in your home connected to the service.
Why it matters for you: Every smart device in your home — from speakers to cameras — is another way hackers can get into your network.
Tips to Protect IoT Devices
Change default usernames and passwords. Never leave factory settings in place — attackers scan for these known defaults.
Disable unnecessary features. Turn off remote access, UPnP (Universal Plug and Play), or voice activation if you don’t need them.
Monitor device activity. Keep an eye on your router logs or use network monitoring tools to detect unusual traffic from IoT devices.
Buy from reputable brands. Choose devices with a history of providing timely security updates and strong privacy practices.
A good rule of thumb: If a device connects to the internet, secure it like a computer.
8. Over 8 million DDoS attacks were recorded in just the first half of 2025
Netscout recorded more than 8 million DDoS attacks in the first half of 2025 alone, and security researchers say the threat is only growing. StormWall, a DDoS protection firm, projects it will mitigate up to 58 million attacks in 2026, nearly three times the number in 2025.
So what exactly is a DDoS attack? Think of it like a traffic jam engineered on purpose. Hackers flood a website or server with so much fake traffic that it slows to a crawl or shuts down completely. Sometimes the goal is just to cause chaos, like knocking a competitor’s game server offline. But often it’s a cover for something worse, like sneaking malware onto a network to steal passwords or banking information.
Several trends are fueling the surge. Experts warn that AI is playing a growing role in enabling DDoS attacks, with analysts predicting 2026 could be a record-setting year for both attack volume and peak attack size. Ransomware groups, facing declining profits in 2025, are also increasingly bundling DDoS capabilities into their offerings, meaning more bad actors than ever will have these tools at their disposal. (DIGIT, Feb 2026) And the geopolitical picture isn’t helping: ongoing tensions involving Russia and Iran could drive a new wave of attacks targeting the U.S., EU, Ukraine, and Israel in 2026. (Intelligentciso, Feb 2026)
These attacks don’t just hit big corporations. Gaming platforms, small businesses, and even home networks can be targeted. The devices doing the attacking are often ones you’d never suspect, like hijacked smart TVs and routers.
Why it matters for you: You don’t have to run a business to be affected. Gamers and streamers can get knocked offline mid-session, and anyone whose home network gets caught in the crossfire could have personal data exposed. Keeping your devices updated (including your smart TV and IoT devices) is one of the simplest ways to avoid becoming part of the problem.
Tips to Protect Against DDoS Attacks for Home Users & Gamers
Use a gaming VPN. A VPN hides your real IP address, making it much harder for attackers to flood your connection directly.
Change your IP address. If you suspect you’re being targeted, reboot your modem/router or request a new IP from your ISP.
Don’t share your IP. Avoid posting your IP online, and be cautious when joining unofficial servers, voice chats, or P2P apps that may expose it.
Enable router-level protections. Many modern routers offer built-in firewalls, intrusion detection, or “DoS protection” features you can toggle on.
Use wired connections when possible. A direct Ethernet connection is less prone to disruption and packet loss during traffic spikes than Wi-Fi.
Coordinate with your ISP. ISPs can sometimes detect and block attack traffic before it reaches your home network — ask about DDoS protection services.
A good rule of thumb: Protect your IP address like you protect your gamer tag — if attackers can’t find you, they can’t flood you.
9. Ransomware complaints increased by 9% year over year.
In the 2024 IC3 (Internet Crime Complaint Center) data, the FBI reported a 9% year-over-year increase in ransomware complaints to IC3. The same report reveals that Akira was the most reported ransomware variant affecting critical infrastructure, with LockBit as the second most reported threat, followed by RansomHub, FOG, and PLAY. IC3 also identified 67 new ransomware variants in 2024, underscoring the rapid evolution of the threat landscape.
It is reported that 67 new ransomware variants were identified in 2024, highlighting the evolving nature of cyber threats despite law enforcement efforts.
Tips to prevent ransomware attacks
Ransomware often starts with a phishing email, a weak password, or an unpatched device. A few basic habits can dramatically reduce your risk.
- Back up your files regularly (and keep one backup offline). If ransomware locks your data, a recent backup is your best option for recovery.
- Keep devices, apps, and operating systems up to date. Many ransomware attacks exploit known software vulnerabilities that updates are designed to fix.
- Be cautious with links, attachments, and downloads. Don’t open unexpected files or click links in emails, texts, or pop-ups — especially if they create urgency.
- Use strong passwords and enable multi-factor authentication (MFA). MFA helps protect your accounts even if a password is stolen.
- Use reputable antivirus and security software. Good security tools can help detect suspicious behavior and block malicious files before they run.
- Limit admin access on everyday accounts. Using a standard user account instead of an administrator account can reduce the damage malware can do.
Rule of thumb: Back it up, update it, and don’t click anything you weren’t expecting.
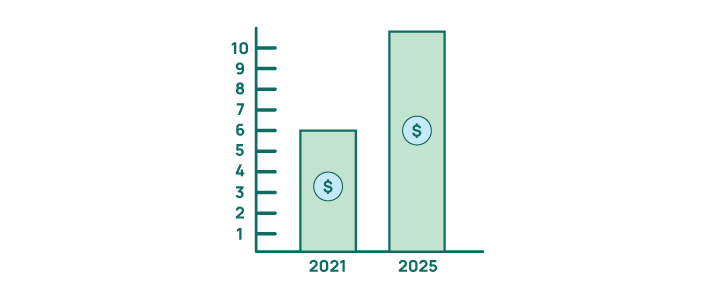
10. Global cybercrime is estimated to cost $10.5 trillion annually
Cybercrime Ventures estimates it costs businesses and individuals over $10.5 trillion annually. You read that right. Trillion. That’s up from $6 trillion in 2021, reports Cybercrime Magazine. It’s more profitable than the combined trade of illegal drugs.
Why it matters for you: That massive figure isn’t just about corporations — it includes the money and data stolen from everyday consumers like you.
Tips to Reduce or Avoid Cybercrime
Use secure payment methods. Stick to credit cards, digital wallets (Apple Pay, Google Pay), or other secure platforms instead of debit cards when shopping online.
Shop only on trusted websites. Look for “https://” in the address bar and avoid deals from unknown sites or random links on social media.
Freeze your credit when not applying for loans. A free credit freeze prevents criminals from opening accounts in your name.
A good rule of thumb: If a deal, message, or request feels urgent or too good to be true, step back and verify — criminals rely on rushed clicks.
Master Cyber Hygiene Checklist
No matter the type of cyber threat — phishing, weak passwords, ransomware, or DDoS — these core practices form your first line of defense.
- Use strong, unique passwords
- At least 12–16 characters, with a mix of letters, numbers, and symbols.
- Never reuse passwords across accounts.
- Enable multi-factor authentication (MFA)
- Add an extra layer of protection, especially for banking, email, and social media accounts.
- Add an extra layer of protection, especially for banking, email, and social media accounts.
- Use a password manager
- Generate and store complex, unique passwords without having to remember them all.
- Generate and store complex, unique passwords without having to remember them all.
- Keep devices and software updated
- Apply patches for operating systems, browsers, apps, and firmware to close security gaps.
- Apply patches for operating systems, browsers, apps, and firmware to close security gaps.
- Secure your home Wi-Fi
- Use WPA2/WPA3 encryption, update router firmware, and change default router passwords.
- Use WPA2/WPA3 encryption, update router firmware, and change default router passwords.
- Encrypt sensitive data
- Use built-in encryption like BitLocker (Windows) or FileVault (macOS) to protect files if devices are stolen.
- Use built-in encryption like BitLocker (Windows) or FileVault (macOS) to protect files if devices are stolen.
- Back up important data
- Maintain both cloud and offline backups to guard against ransomware or accidental loss.
- Maintain both cloud and offline backups to guard against ransomware or accidental loss.
- Be cautious on public Wi-Fi
- Avoid logging into sensitive accounts, or use a VPN to secure your connection.
- Avoid logging into sensitive accounts, or use a VPN to secure your connection.
- Use mobile security software
- Scan for malware and block high-risk apps on smartphones and tablets.
- Scan for malware and block high-risk apps on smartphones and tablets.
- Limit personal information online
- Avoid oversharing on social media — attackers use birthdays, locations, and job details for social engineering.
- Avoid oversharing on social media — attackers use birthdays, locations, and job details for social engineering.
- Turn off unused services
- Disable Bluetooth, NFC, or location sharing when you don’t need them.
- Disable Bluetooth, NFC, or location sharing when you don’t need them.
- Log out of accounts on shared/public devices
- Prevent unauthorized access if someone else uses the device after you.
Stay Smart, Stay Secure
Cybercrime isn’t slowing down — it’s scaling up. From phishing emails and weak passwords to DDoS attacks and vulnerable IoT devices, the threats are everywhere. But here’s the good news: most breaches can be prevented with everyday habits.
By practicing stronger password hygiene, keeping your software and devices updated, being skeptical of suspicious links, and protecting your network with tools like VPNs and encryption, you drastically reduce your chances of becoming part of the $10.5 trillion in cybercrime.
Cybersecurity isn’t just for businesses or tech experts — it’s for anyone who shops, banks, plays games, or simply browses online. The more proactive you are, the fewer doors you leave open for attackers.
Cybersecurity Facts and Stats FAQs
The top 10 cybersecurity threats include phishing, weak passwords, ransomware, malware, data breaches, DDoS attacks, IoT vulnerabilities, insider threats, social engineering scams, and outdated software exploits. Staying aware of these threats helps users recognize common attack patterns and protect themselves more effectively.
Cyber security facts highlight how everyday habits — like clicking a suspicious link or reusing a password — contribute to most breaches. Knowing the basics empowers users to make smarter online decisions, whether it’s enabling multi-factor authentication, updating software, or avoiding unsafe Wi-Fi networks.
Some eye-opening facts about cybersecurity include: cybercrime costs are expected to exceed $10.5 trillion annually in 2025, about 68% of breaches involve human error, and nearly one in four smartphones has a high-risk app installed. These facts show how widespread cybercrime has become — and why prevention matters.
Home users should know how to:
- Use strong, unique passwords for each account.
- Protect home Wi-Fi with WPA2/WPA3 encryption.
- Avoid oversharing personal info online.
- Back up files to recover from ransomware or hardware failure.
- Consider a VPN for privacy and safer gaming.
Individuals are very much at risk. Attackers often target consumers with phishing scams, identity theft attempts, and financial fraud. In fact, most cyberattacks start with human error — proving that everyday users play a big role in cybersecurity defenses.
IoT devices are growing rapidly — from 16.6 billion in 2023 to 18.8 billion in 2024, with projections of about 40 billion by 2030 (IoT Analytics). More connected devices means more opportunities for hackers to target your home network and personal data.
Every smart device, like cameras, speakers, and thermostats, can be a potential entry point if it isn’t secured.
How to protect IoT devices:
- Change default usernames and passwords
- Disable unused features (like remote access or UPnP)
- Monitor device activity on your router and network
- Choose reputable brands with regular security updates
Rule of thumb: If it connects to the internet, secure it like a computer.
Yes. In the FBI’s 2024 IC3 data, adults age 60+ reported 147,127 complaints and about $4.885 billion in losses, the highest losses of any age group. The report also shows that this age group lost $385,001,099 to Business Email Compromise (BEC) scams alone (a major email-based fraud category).
BEC scams typically involve criminals impersonating a trusted person or organization by email to trick victims into sending money or sensitive information.
About 1 in 3 internet users (32%) reported using a VPN in a 2025 Security.org survey of U.S. consumers. That’s a smart trend, because a VPN is one of the easiest ways to improve online privacy and security.
A VPN (virtual private network) helps protect your data by encrypting your internet traffic and masking your IP address, which makes it harder for others to track your activity or identify your location.
Why it matters for you: A VPN can help protect your privacy on public Wi-Fi, reduce ISP tracking, and add an extra layer of security while gaming or browsing online.
Tips for using a VPN:
- Choose nearby servers for better speed (or other regions for added privacy and access needs)
- Use a reputable VPN provider with a clear no-logs policy and strong security standards
- Avoid free VPNs that may collect or sell your data
Rule of thumb: If you’re online in public or gaming with strangers, connect to a VPN first.
Business Email Compromise (BEC) is a scam where criminals impersonate a trusted person or organization (such as a boss, vendor, or company representative) to trick someone into sending money or sensitive information.
According to the FBI’s 2024 IC3 report, BEC generated 21,442 complaints in 2024 and caused about $2.77 billion in reported losses, making it the second-costliest cybercrime category by losses. Over 2022–2024, reported BEC losses totaled about $8.46 billion (roughly $8.5 billion), showing how persistent and expensive this threat remains.
AI is now helping both attackers and defenders move faster.
On the threat side, Microsoft’s 2025 Digital Defense Report says attackers are using techniques like AI-automated phishing, while also highlighting deepfake fraud and the risk of AI-enabled automated attack workflows (such as reconnaissance, vulnerability scanning, and exploitation). CrowdStrike’s 2025 threat reporting also says adversaries used GenAI to strengthen social engineering, including fake profiles, phishing content, and deepfake-style deception.
On the defense side, AI red teaming is a proactive cybersecurity practice where organizations simulate adversarial behavior to uncover weaknesses before real attackers do. A 2025 scoping review on AI-driven cyberattacks found AI can automate and accelerate attack activity, and noted that AI-based red-team techniques can help simulate cybercrime scenarios for testing. AI red teaming is when security experts use AI to safely “test” systems the way a real hacker might, to find and fix weaknesses before they can be exploited.